For a while now we’ve known that one of the caveats for using shared mailboxes is that when you delete items from the shared mailbox they end up in the user’s ‘Deleted Items’ folder and when you send email as the shared mailbox it similarly ends up in the user’s ‘Sent Items’ folder. For a bit we had a tweak for the ‘Sent Items’ problem but Microsoft stopped supporting it in Exchange 2013.
Because of recent questions about these subjects I’ve looked into it again and found fixes for both situations.
Sent Items
Awhile back I found an Exchange cmdlet, Set-MailboxSentItemsConfiguration, that would allow you to change a setting that when you send email from a shared mailbox you could control whether that sent email would be copied to your Sent Items folder (default), to the Sent Items folder of the shared mailbox, or to both. Shortly after finding that tweak UFX was upgraded to Exchange 2013 and it stopped working since it was no longer supported.
After enough complaining Microsoft added that feature back in to Office 365 and Exchange 2013 CU 9… which was back in Sept 2015. Looks like we should have looked at this sooner.
There are only two settings now however. You can have the sent email goto the Sent Items folder of the user mailbox or to the folder of both the user and the shared mailbox. It is also not done by a dedicated cmdlet anymore but is a configuration option to set-mailbox:
PS C:\> set-mailbox [identity] –MessageCopyForSentAsEnabled [$True | $False] PS C:\> set-mailbox [identity] –MessageCopyForSendOnBehalfEnabled [$True | $False]
Default setting is $False (sent email goes to the ‘Sent Items’ folder of the user).
It is important to note that it HAS to be a shared mailbox. There may be mailboxes that are set as resource, room, or user mailboxes that are used like a shared mailbox where this setting will not work. For instance, I was unable to set this on a service account user mailbox that is also shared.
Deleted Items
Similar to the Sent Items problem, when you delete an item from a shared mailbox in Outlook it goes to the Deleted Items folder of your primary user mailbox and not to the Deleted Items folder of the shared mailbox itself. Turns out there is a way to change this behavior on a workstation but it involves registry hacking (a KB also has a fixit app that could be run on a workstation).
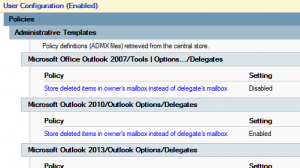
However, chances are you want to apply this to all your managed workstations. In that case there is a very easy Group Policy you can apply. Enable the Store deleted items in owner’s mailbox instead of delegate’s mailbox policy found under User Configuration as follows:
\\User Configuration\Policies\Administrative Templates\Microsoft Outlook [2010 | 2013 | 2016]\Outlook Options\Delegates